A new JSCEAL malware campaign mimics 50 popular crypto platforms according to Check Point Research. The operation uses malicious advertisements to distribute fake applications targeting users.
An estimated 10 million people globally have been exposed to attacks. The campaign leverages compiled JavaScript files to steal cryptocurrency wallets and credentials effectively.
Malicious advertisement campaign reaches 10 million users
The JSCEAL campaign exposed around 35,000 malicious ads in the first half of 2025. They themselves garnered millions of views in the European Union. Check Point Research is of the view that around 10 million people viewed these ads worldwide.
Malicious material was shared by ill-intentioned actors on hijacked accounts or fresh profiles. Promoted posts assisted in the distribution of fake advertisements on social media. The advertisements mostly discussed cryptocurrencies, tokens, and banks.
The campaign run using almost 50 various financial institutions with spoofed applications. The bad actors registered domain names under some naming conventions for redirection. The top-level domains contained a .com extension in accordance with corresponding terminology.
Patterns in the domain included app, download, desktop, PC, and window versions. Each word was used singly or in a plural sense in the domains. Combinatorics show that there are 560 unique domain names that are in compliance with the rules.
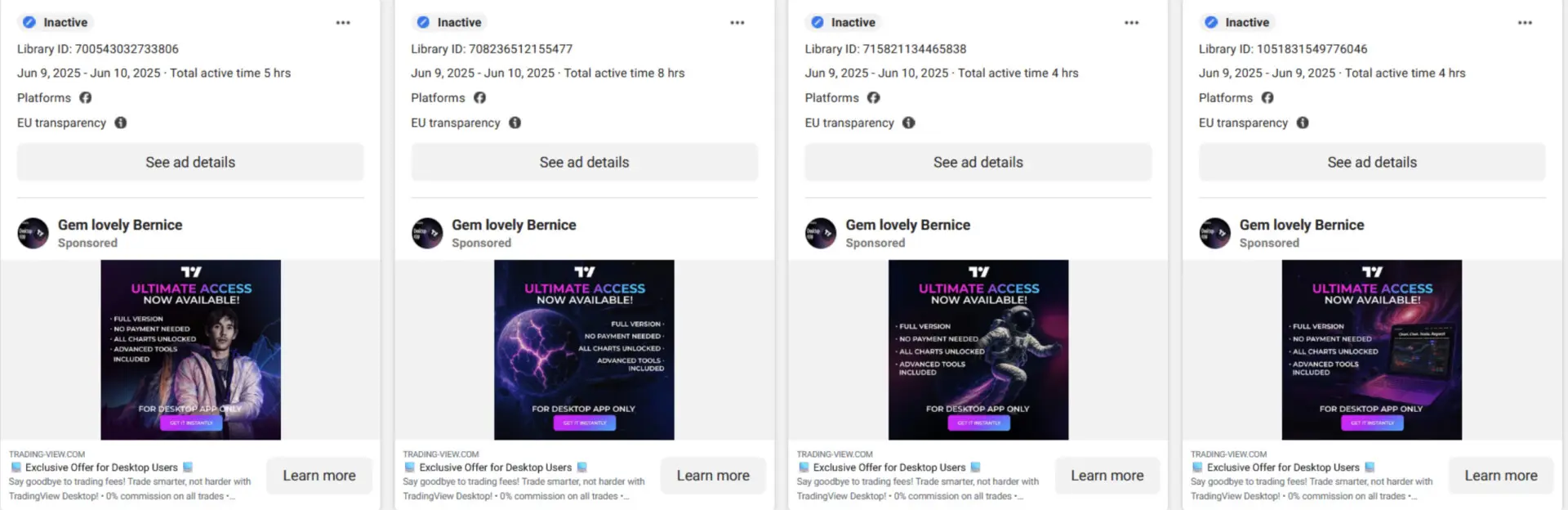 Malicious ads on Facebook, Source: Check Point
Malicious ads on Facebook, Source: Check Point
Only 15% of potential domains appeared registered at publication time. Redirection chains filtered targets based on IP address and referrer sources.
Victims outside the desired ranges received decoy websites instead of malicious content. Facebook referrers were required for successful redirection to fake pages. The filtering system helped attackers avoid detection while they reached their target victims.
Meta’s Ad Library provided estimates for advertisement reach within the EU. Conservative calculations assume each advertisement reached 100 users minimum. The campaign’s total reach exceeded 3.5 million within the European Union boundaries.
Global reach could easily exceed 10 million, considering non-EU countries. Asian crypto and financial institutions were also impersonated in the campaigns.
Campaign uses sophisticated deception tactics to avoid detection
JSCEAL campaign uses certain anti-evasion methods, resulting in extremely low detection rates. The malware remained undetected for extended periods, according to Check Point analysis. These sophisticated techniques help attackers bypass traditional security measures across multiple platforms.
Victims clicking on malicious advertisements get directed to legitimate-looking fake websites. The fake sites encourage downloading malicious applications that appear authentic. Attackers design websites to closely mimic real cryptocurrency platform interfaces.
The malware uses the simultaneous operation of the website and installation software. This dual approach complicates analysis and detection efforts for security researchers. Individual components appear harmless when examined separately, making detection challenging.
This deception tactic convinces victims that they installed authentic software. Meanwhile, the malware operates in the background, collecting sensitive information without users’ knowledge.
The campaign targets cryptocurrency users specifically through platform impersonation tactics. Attackers focus on popular trading applications and wallet software. Users seeking legitimate crypto tools were the most susceptible to the campaign.
Check Point researchers describe the detection evasion as highly effective. Traditional security software struggles to identify threats using these methods. The combination of legitimate-looking interfaces and hidden malware creates dangerous scenarios.
Malware harvests crypto-related data and user credentials systematically
The malware’s primary purpose involves gathering sensitive information from infected devices. Attackers collect data to access cryptocurrency accounts and steal digital assets. Information harvesting occurs automatically without requiring user interaction or awareness.
JSCEAL captures keyboard inputs, revealing passwords and authentication credentials across applications. The keylogging functionality records everything users type, including crypto wallet passwords. They also target Telegram account information for potential account takeover.
They also harvest browser cookies showing victims’ frequently visited websites and preferences. Autocomplete passwords stored in browsers are also accessible to threat actors.
Your crypto news deserves attention - KEY Difference Wire puts you on 250+ top sites




