A Russian Hacking Group Is Using Fake Versions of MetaMask to Steal $1M in Crypto
The Russian hacking group GreedyBear has scaled up its operations in recent months, using 150 “weaponized Firefox extensions” to target international and English-speaking victims, according to research from Koi Security.
Publishing the results of its research in a blog, U.S. and Israel-based Koi reported that the group has “redefined industrial-scale crypto theft,” using 150 weaponized Firefox extensions, close to 500 malicious executables and “dozens” of phishing websites to steal over $1 million within the past five weeks.
Speaking to Decrypt, Koi CTO Idan Dardikman said that the Firefox campaign is “by far” its most lucrative attack vector, having “gained them most of the $1 million reported by itself.”
This particular ploy involves creating fake versions of widely downloaded crypto wallets such as MetaMask, Exodus, Rabby Wallet, and TronLink.
GreedyBear operatives use Extension Hollowing to bypass marketplace security measures, initially uploading non-malicious versions of the extensions, before updating the apps with malicious code.
They also post fake reviews of the extensions, giving the false impression of trust and reliability.
But once downloaded, the malicious extensions steal wallet credentials, which in turn are used to steal crypto
Not only has GreedyBear been able to steal $1 million in just over a month using this method, but they have greatly ramped up the scale of their operations, with a previous campaign–active between April and July of this year–involving only 40 extensions.
The group’s other primary attack method involves almost 500 malicious Windows executables, which it has added to Russian websites that distribute pirated or repacked software.
Such executables include credential stealers, ransomware software and trojans, which Koi Security suggests indicates“a broad malware distribution pipeline, capable of shifting tactics as needed.”
The group has also created dozens of phishing websites, which pretend to offer legitimate crypto-related services, such as digital wallets, hardware devices or wallet repair services.
GreedyBear uses these websites to coax potential victims into entering personal data and wallet credentials, which it then uses to steal funds.
“It is worth mentioning that the Firefox campaign targeted more global/English-speaking victims, while the malicious executables targeted more Russian-speaking victims,” explains Idan Dardikman, speaking to Decrypt.
Despite the variety of attack methods and of targets, Koi also reports that “almost all” GreedyBear attack domains link back to a single IP address: 185.208.156.66.
According to the report, this address functions as a central hub for coordination and collection, enabling GreedyBear hackers “to streamline operations.”
Dardikman saidthat a single IP address “means tight centralized control” rather than a distributed network.
“This suggests organized cybercrime rather than state sponsorship–government operations typically use distributed infrastructure to avoid single points of failure,” he added. “Likely Russian criminal groups operating for profit, not state direction.”
Dardikman said that GreedyBear is likely to continue its operations and offered several tips for avoiding their expanding reach.
“Only install extensions from verified developers with long histories,” he said, adding that users should always avoid pirated software sites.
He also recommended using only official wallet software, and not browser extensions, although he advised moving away from software wallets if you’re a serious long-term investor.
He said, “Use hardware wallets for significant crypto holdings, but only buy from official manufacturer websites–GreedyBear creates fake hardware wallet sites to steal payment info and credentials.”
Disclaimer: The content of this article solely reflects the author's opinion and does not represent the platform in any capacity. This article is not intended to serve as a reference for making investment decisions.
You may also like
DiDi has become a digital banking giant in Latin America
DiDi has successfully transformed into a digital banking giant in Latin America by addressing the lack of local financial infrastructure, building an independent payment and credit system, and achieving a leap from a ride-hailing platform to a financial powerhouse. Summary generated by Mars AI. This summary was produced by the Mars AI model, and its accuracy and completeness are still being iteratively improved.

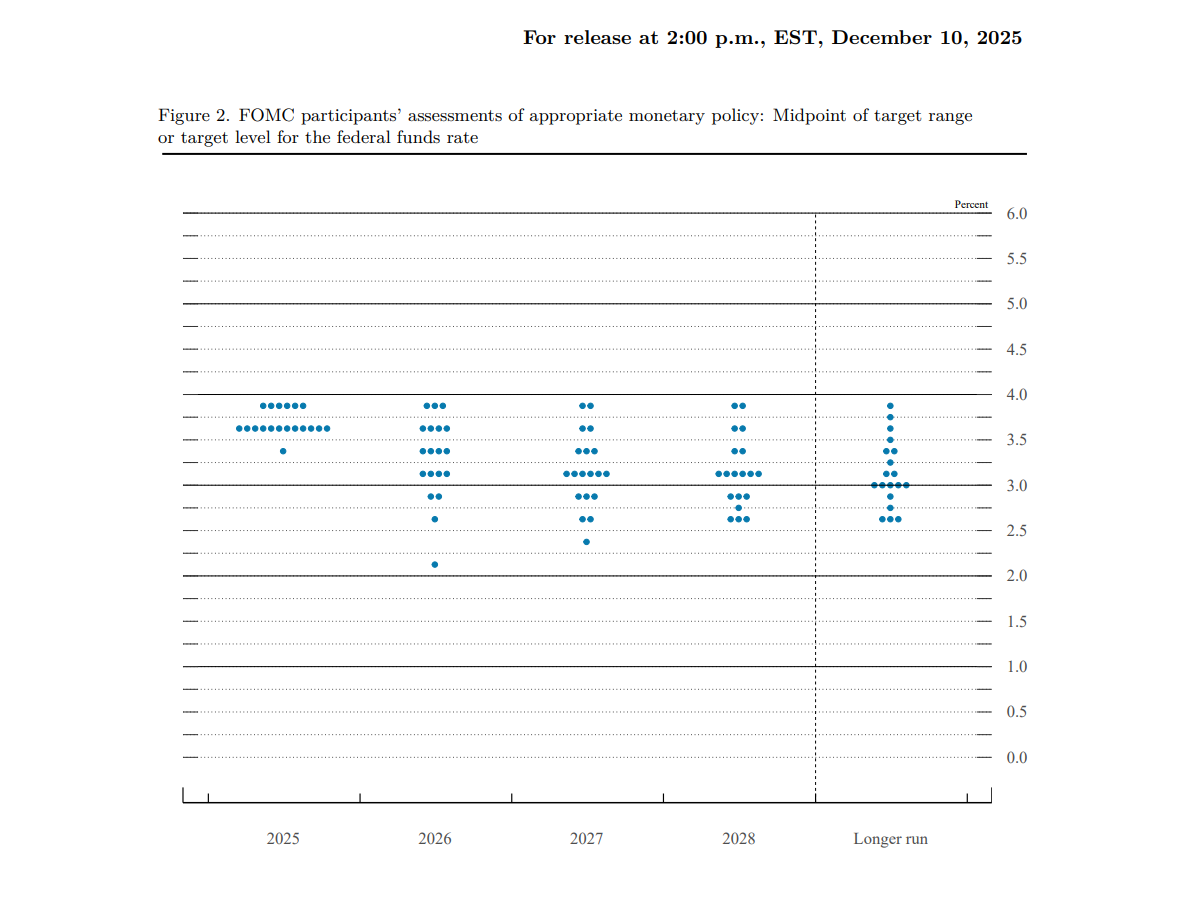
Fed rate cuts in conflict, but Bitcoin's "fragile zone" keeps BTC below $100,000
The Federal Reserve cut interest rates by 25 basis points, but the market interpreted the move as hawkish. Bitcoin is constrained by a structurally fragile range, making it difficult for the price to break through $100,000. Summary generated by Mars AI This summary was generated by the Mars AI model, and the accuracy and completeness of its content are still being iteratively updated.

Full text of the Federal Reserve decision: 25 basis point rate cut, purchase of $4 billion in Treasury bills within 30 days
The Federal Reserve cut interest rates by 25 basis points with a 9-3 vote. Two members supported keeping rates unchanged, while one supported a 50 basis point cut. In addition, the Federal Reserve has restarted bond purchases and will buy $40 billion in Treasury bills within 30 days to maintain adequate reserve supply.
HyENA officially launched: Perp DEX supported by Ethena and based on USDe collateral goes live on Hyperliquid
The launch of HyENA further expands the USDe ecosystem and brings institutional-grade margin efficiency to the on-chain perpetuals market.
